Digital Infrastructure, Cloud and Security
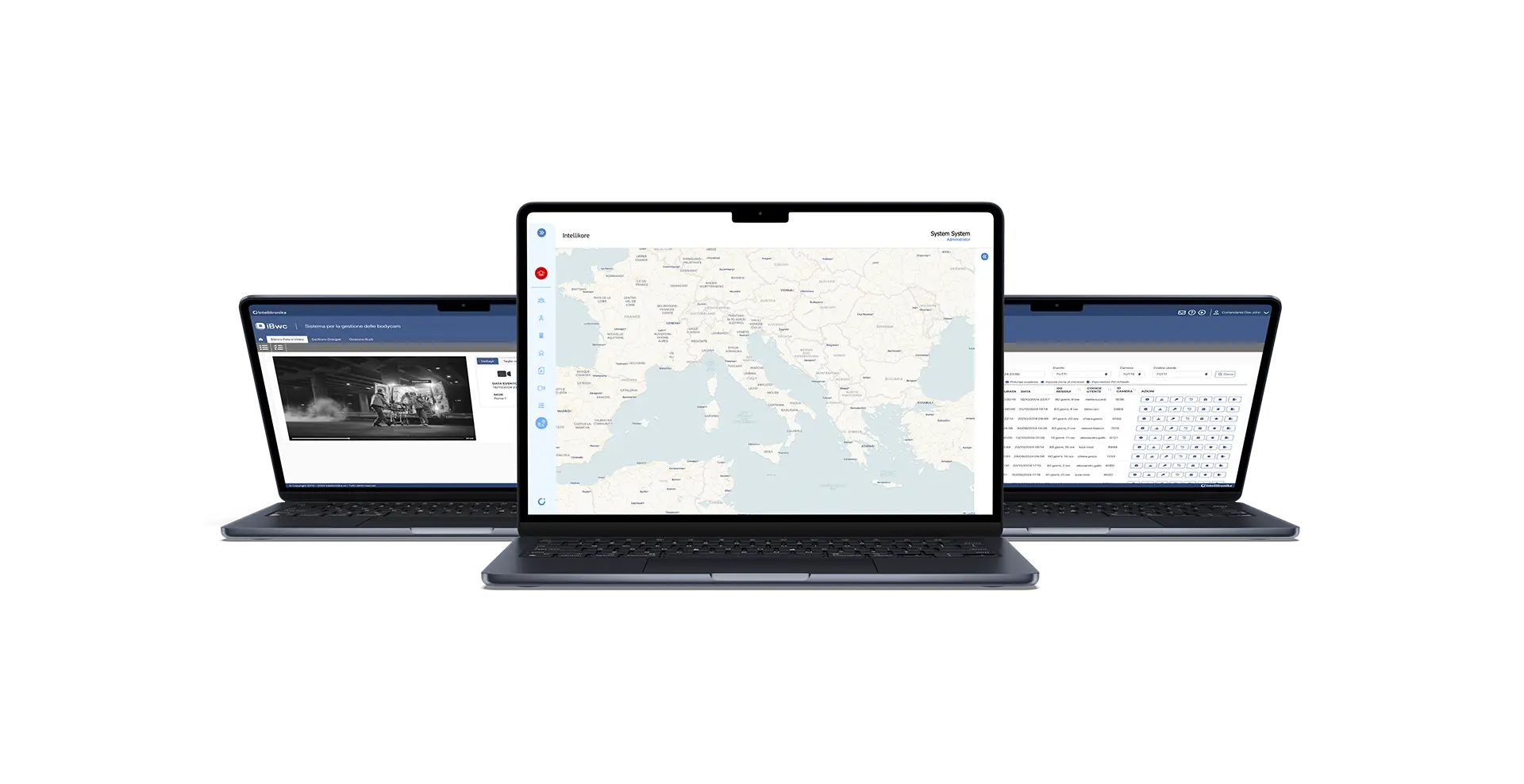
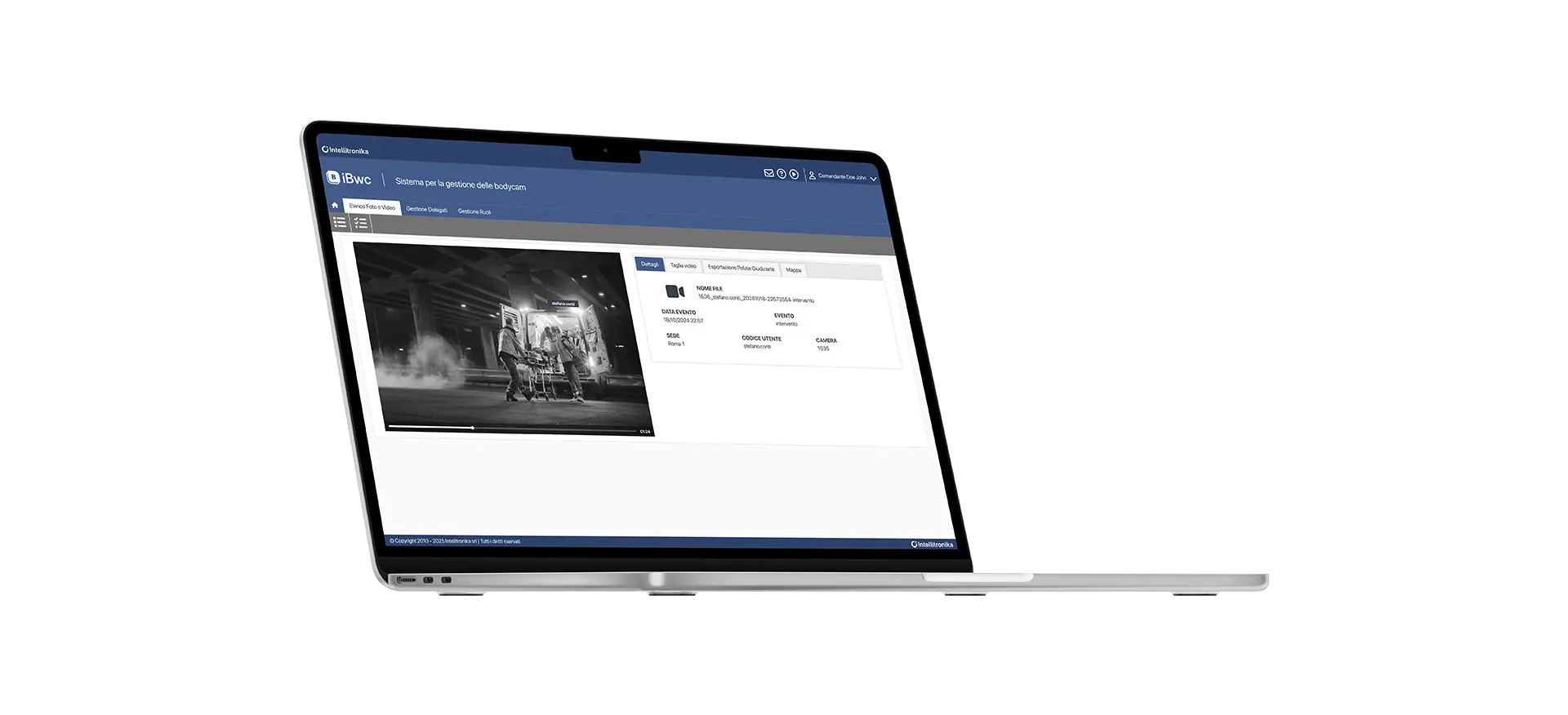
Intellitronika designs secure and resilient digital infrastructures, built to support critical systems and to operate both on-premise and in cloud environments.
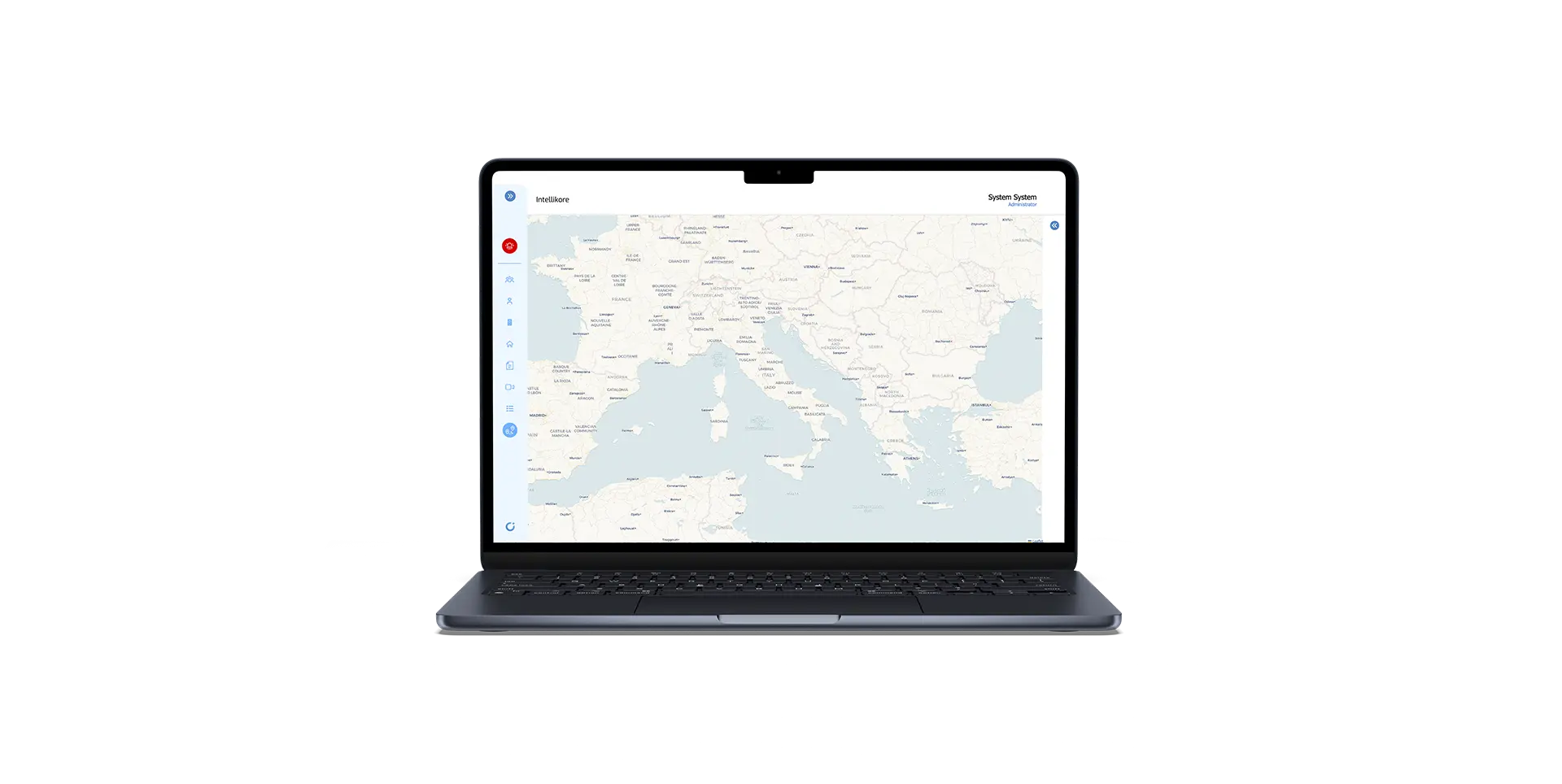
Infrastructure, migration and security activities enable organizations to evolve their information systems while maintaining control, operational continuity and data protection. Thanks to its specialized teams, Intellitronika supports institutions and organizations in designing digital architectures capable of managing sensitive data, distributed field devices and highly critical services, ensuring consistency between operational requirements, security and technological sustainability.
The adopted approach integrates application migration, protection of peripheral infrastructures and digital identity governance into a single architectural design. The solutions are designed to operate in on-premise, cloud or hybrid environments, in order to meet different needs related to data control, regulatory compliance and operational performance.
The use of advanced security models, behavioral analysis tools and methodologies based on Zero Trust, end-to-end encryption and artificial intelligence makes it possible to reduce the attack surface, prevent threats and strengthen the overall resilience of systems.